How to configure SolusVM noVNC console use via Cloudflare Passthrough
Are you using SolusVM and Cloudflare and just want to get noVNC working, right now?
Here’s how to configure the SolusVM noVNC console to work from behind Cloudflare:
- In SolusVM, go to “General -> Settings -> Other”
- Configure the “noVNC socket port” to 8443.
At that point, the noVNC console should just work in 90% of cases. Keep reading to find out what this change does, why this change is necessary, and what to do in the other 10% of cases.
Table of Contents
First, some background
One of the most important things to consider when working in the hosting industry is the security of your servers. Control panels such as SolusVM are a popular attack target, and so securing these is especially important. Cloudflare has emerged as a popular and effective line of defense for web servers and the websites running on them, including control panels like SolusVM.
To provide this protection, Cloudflare acts as a reverse web proxy. This means, your website’s domain will point to a Cloudflare based IP, where a Cloudflare server will filter out attacks and malformed requests. For any legitimate requests, the Cloudflare server will pass those to your web server, and relay the result back to the internet user. By acting as a middle man, Cloudflare helps keep your web server’s IP address a secret. This in turn makes it more difficult for attackers to target your server for exploit and attack.
While a helpful service, sometimes a direct connection between your server and internet clients is necessary. One example of this is the built-in noVNC console in SolusVM. Since this VNC console provides access to essential features of your VPS, it is important that the built in utility works properly. By default, enabling Cloudflare for the domain associated with your SolusVM panel will make this impossible. Today’s article will show you how to configure Cloudflare passthrough so that you can continue using the SolusVM noVNC console, while still enjoying the security benefits Cloudflare has to offer.
Why does Cloudflare break noVNC?
The main issue comes from what Cloudflare was designed to do: proxy HTTP and HTTPS requests. These requests normally happen on TCP port 80 and TCP port 443, respectively. Other ports are typically used for all kinds of services that Cloudflare is not compatible with. Therefore, Cloudflare will ignore any traffic that is targeting ports not typically used for HTTP / HTTPS traffic. As the default port for SolusUI is 7706, this means by default, this traffic will be blocked.
The good news is that although this traffic is on a custom port, it is standard HTTPS / SSL traffic that Cloudflare is capable of handling. We just need to redirect this traffic to a port where Cloudflare knows what to do with it.
How to fix the problem
Cloudflare has a list of ports that it will forward through as HTTP and HTTPS traffic. For your reference, here are the HTTPS / SSL ports that Cloudflare allows as of the time this was written:
- 443
- 2053
- 2083
- 2087
- 2096
- 8443
Port 443 is already in use for general web traffic, and also Cloudflare does caching against requests to this port. For both of those reasons, we need to use one of the other ports provided. The other ports allow for passthrough without caching, and might not be in use by conflicting services already. By setting the VNC console to work on one of these ports, Cloudflare knows to simply pass the traffic directly to your SolusVM UI instance unchanged.
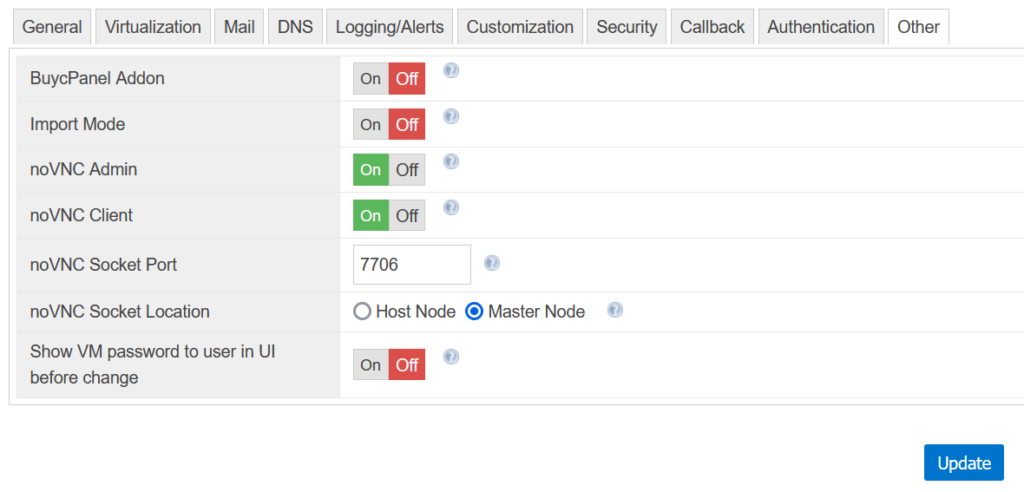
First, go to your noVNC console settings. These can be found under “General -> Settings -> Other”. Your default noVNC console settings should look something like in the image below. Your options may be slightly different based on what version of SolusVM you are currently using.
All we have to do is pick an appropriate, unused HTTPS port for your services. Once you’ve decided on one, update SolusVM’s VNC port to that unused port. In this example, we’ve decided to use 8443:
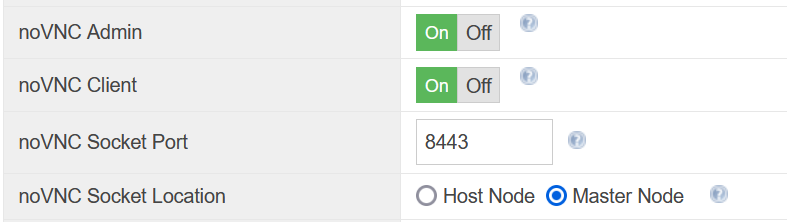
Please keep in mind that some of the Cloudflare supported port numbers are used by other popular software, so you may need to do some trial and error to find an unused port you can use. This will vary depending upon what other services are active for your website domain.
For example, if your domain’s website is hosted on a cPanel server, you need to avoid the ports that cPanel is already using. cPanel uses ports 2083, 2087, and 2096 for HTTPS connections to its cPanel, WHM, and webmail control panels respectively, so we recommend against using these ports for noVNC. That leaves ports 2053 and 8443 as the ones I’d recommend trying first.
Did port 8443 not work for you?
Port 8443 is used by the Apache Tomcat server, so if you’re using Tomcat, you might have to avoid 8443 as well. If you’re using cPanel, the only port left to try is 2053.
If you’re sure you’re not using cPanel for your domain, then any of the ports mentioned as used by cPanel – 2083, 2087, and 2096 – should work just fine. To check if your cPanel ports are in use, open your web browser, type https, your servers IP address, followed by the port number, such as:
Of course, replacing 127.0.0.1 with your server IP address. If nothing loads, then the port should not be in use. You can then safely use the port in your noVNC configuration.
You’re done!
With this one simple change, you can provide your clients access to an important tool within Solus while at the same time protecting your domain from attack.
As always, IOFLOOD loves servers, and if you do too, we hope you’ll join us! If you’re interested in hosting with a company that loves servers and treats customers fairly, contact us. We can be reached at sales[at]ioflood.com, or you can check out our dedicated servers page for more info.